In the realm of cybersecurity, firewalls have long been a cornerstone of network protection. Traditional firewalls, often deployed as physical appliances or software on-premises, were designed to monitor and control traffic between internal networks and the broader internet. They operated primarily at the network perimeter, using rule-based policies to allow or block traffic based on IP addresses, ports, and protocols. However, with the advent of cloud computing and the increasing complexity of modern IT environments, traditional firewalls faced significant limitations. They struggled to adapt to the dynamic nature of cloud workloads, the need for scalable infrastructure, and the growing threat landscape.
What is a Cloud Firewall?
Enter cloud firewalls, a next-generation solution tailored for the cloud-native era. Cloud firewalls leverage cloud infrastructure's scalability, flexibility, and agility to provide robust security controls. Unlike their traditional counterparts, cloud firewalls are designed to operate within the cloud environment, integrating seamlessly with cloud platforms and services. They offer advanced threat detection capabilities, real-time monitoring, and automated policy enforcement, making them an essential component of modern network security strategies.
The shift towards cloud computing has transformed the way organizations operate. Hybrid and multi-cloud environments are now the norm, with enterprises leveraging multiple cloud providers to optimize performance, cost, and innovation. In this context, traditional security models are no longer sufficient. Cloud firewalls play a crucial role in addressing the unique challenges of cloud environments:
- Scalability: Cloud firewalls can dynamically scale to handle varying levels of traffic, ensuring consistent performance even during peak loads.
- Flexibility: They integrate seamlessly with cloud platforms, allowing organizations to deploy security controls across multiple environments without compromising functionality.
- Advanced Threat Detection: Cloud firewalls, with built-in intrusion prevention systems (IPS) and threat intelligence feeds, can detect and mitigate sophisticated threats in real-time.
- Compliance: Cloud firewalls help organizations meet regulatory requirements such as GDPR, HIPAA, and PCI-DSS by providing granular control over data access and ensuring secure data handling practices.
How Cloud Firewalls Enhance Your Network Security
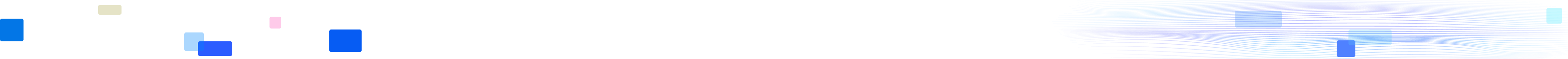
1. Key Architectural Components
Distributed Architecture for Cloud-Native Environments
Cloud firewalls are built on a distributed architecture, designed to operate natively within the cloud. This architecture allows them to leverage the inherent benefits of cloud infrastructure, such as elasticity, high availability, and fault tolerance. Distributed components are deployed across multiple regions and availability zones, ensuring that security controls are always available and can handle large-scale traffic without performance degradation.
Integration with Public/Private/Hybrid Cloud Platforms
One of the key strengths of cloud firewalls is their ability to integrate seamlessly with major cloud platforms. Whether an organization uses Amazon Web Services (AWS), Microsoft Azure, Google Cloud Platform (GCP), or a combination of these, cloud firewalls can be deployed to provide consistent security controls. For instance, on AWS, cloud firewalls can be integrated with Virtual Private Cloud (VPC) to protect workloads and data stored within the cloud. Similarly, on Azure, they can be deployed as part of the Azure Security Center to enhance overall security posture. This integration ensures that security policies are enforced consistently across different cloud environments, reducing the risk of security gaps.
Virtual Private Cloud (VPC) vs. SaaS-Based Models
Policy enforcement is a critical aspect of cloud firewall architecture. In cloud-native environments, policy enforcement points can be deployed at various levels, depending on the specific requirements of the organization. For example, within a Virtual Private Cloud (VPC), enforcement points can be set up to monitor and control traffic between different subnets and resources. This ensures that only authorized traffic is allowed to flow within the VPC, protecting against both external and internal threats.
On the other hand, Software-as-a-Service (SaaS) models offer a different approach. In this scenario, cloud firewalls are deployed as a managed service, with policies enforced at the cloud provider's edge. This model is particularly useful for organizations that want to offload the management burden of security controls to a third-party provider. SaaS-based cloud firewalls can provide centralized policy management, real-time threat detection, and automated response capabilities, making them an attractive option for many enterprises.
2. Core Functionalities
Stateful Packet Inspection (SPI) for Cloud Traffic
Stateful Packet Inspection (SPI) is a fundamental feature of cloud firewalls. Unlike stateless firewalls, which only inspect individual packets, SPI maintains a state table that tracks the status of active connections. This allows the firewall to make more informed decisions about allowing or blocking traffic. For example, if a connection is established between two endpoints, the firewall will remember the state of that connection and only allow packets that are part of the established session. This significantly enhances security by preventing unauthorized traffic from entering the network while allowing legitimate traffic to flow smoothly.
Intrusion Prevention Systems (IPS) and Threat Intelligence Feeds
Intrusion Prevention Systems (IPS) are another critical component of cloud firewalls. IPS solutions actively monitor network traffic for signs of malicious activity, such as malware, exploits, and other threats. When suspicious activity is detected, the IPS can take immediate action to block the traffic and alert security teams. To enhance their effectiveness, cloud firewalls often integrate with threat intelligence feeds. These feeds provide real-time information about emerging threats, allowing the firewall to update its detection capabilities and stay ahead of potential attacks.
Application-Layer Filtering (Layer 7 Protection)
Application-layer filtering, also known as Layer 7 protection, is essential for modern cloud environments. Traditional firewalls primarily operate at the network layer (Layer 3) and transport layer (Layer 4), but cloud firewalls, including advanced WAF and WAAS solutions, extend their capabilities to the application layer. This allows them to inspect and control traffic at a more granular level, ensuring that only legitimate application requests are allowed through.
For example, a WAF can inspect HTTP/HTTPS traffic to detect and block SQL injection attacks, cross-site scripting (XSS), and other application-layer threats. These capabilities are essential for safeguarding web applications and APIs, which are often the primary targets of cyberattacks. By integrating WAF into your security stack, you can significantly enhance the protection of your digital assets and reduce the risk of sophisticated application-layer attacks.
Automated Scaling and Elastic Rule Management
One of the key benefits of cloud firewalls is their ability to scale automatically. In dynamic cloud environments, traffic patterns can change rapidly, and security controls need to adapt accordingly. Cloud firewalls can dynamically adjust their resources to handle varying levels of traffic, ensuring that performance remains consistent. Additionally, they offer elastic rule management, allowing security policies to be updated in real-time based on changing threat conditions. This automation reduces the burden on security teams and ensures that security controls are always up-to-date and effective.
3. Deployment Models
Firewall-as-a-Service (FWaaS)
Firewall-as-a-Service (FWaaS) is a popular deployment model for cloud firewalls. In this model, the firewall is provided as a managed service by a third-party provider. FWaaS solutions offer several advantages, including reduced management overhead, centralized policy management, and real-time threat detection. Organizations can leverage the expertise of the provider to deploy and maintain security controls, ensuring that they are always up-to-date with the latest threat intelligence and security best practices. FWaaS is particularly attractive for small and medium-sized businesses that may lack the resources to deploy and manage their own cloud firewalls.
Cloud-Native vs. Third-Party Solutions
When deploying cloud firewalls, organizations have the option of choosing between cloud-native solutions and third-party offerings. Cloud-native firewalls are provided by the cloud platform itself, such as AWS Network Firewall or Azure Firewall. These solutions offer seamless integration with the cloud environment and are optimized for performance and scalability. However, they may lack some of the advanced features and flexibility offered by third-party solutions.
Third-party cloud firewalls, on the other hand, are developed by specialized security vendors and can be deployed across multiple cloud platforms. They often provide more advanced features, such as advanced threat detection, application-layer filtering, and integration with other security tools. However, they may require more effort to integrate with the cloud environment and may come with additional licensing costs.
Hybrid Implementations for On-Premises/Cloud Integration
Many organizations operate in hybrid environments, combining on-premises infrastructure with cloud resources. In such cases, hybrid implementations of cloud firewalls are essential to ensure consistent security controls across both environments. Hybrid cloud firewalls can bridge the gap between on-premises and cloud networks, providing seamless policy enforcement and threat detection. They can be deployed as virtual appliances on-premises or as managed services in the cloud, ensuring that security policies are enforced consistently regardless of where the workload resides.
Security Advantages of Cloud Firewall
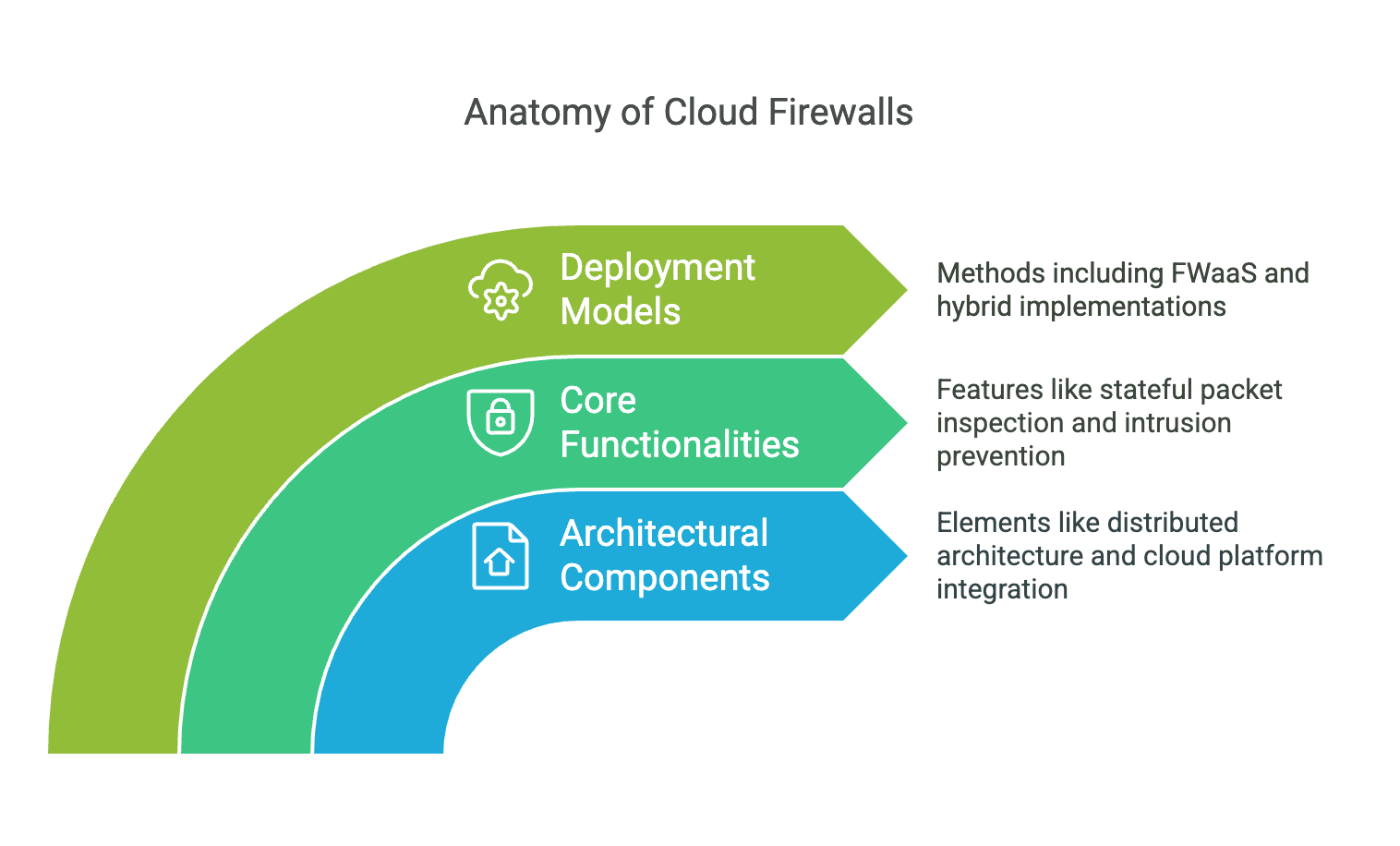
Protection Against DDoS Attacks and Zero-Day Exploits
Cloud firewalls offer robust protection against Distributed Denial of Service (DDoS) attacks and zero-day exploits. DDoS attacks aim to overwhelm a network or application with a flood of traffic, rendering it unavailable. Cloud firewalls can detect and mitigate these attacks in real-time by filtering out malicious traffic and ensuring that legitimate traffic can still reach its destination. Additionally, with built-in intrusion prevention systems and threat intelligence feeds, cloud firewalls can detect and block zero-day exploits, which are previously unknown vulnerabilities that attackers exploit before patches are available.
Compliance Management (GDPR, HIPAA, PCI-DSS)
Compliance with regulatory requirements is a critical concern for many organizations. Cloud firewalls play a vital role in helping enterprises meet compliance standards such as GDPR, HIPAA, and PCI-DSS. By providing granular control over data access, ensuring secure data handling practices, and maintaining detailed logs and audit trails, cloud firewalls help organizations demonstrate compliance with regulatory requirements. For example, in the healthcare sector, HIPAA requires strict controls over the handling of protected health information (PHI). Cloud firewalls can enforce policies to ensure that only authorized personnel have access to PHI, helping organizations avoid costly fines and reputational damage.
Micro-Segmentation for Zero Trust Implementation
Micro-segmentation is a key component of Zero Trust architecture, which assumes that all users and devices are potentially compromised and must be verified before being granted access. Cloud firewalls can enforce micro-segmentation policies, dividing the network into smaller, isolated segments. This ensures that even if one segment is compromised, the attacker cannot easily move laterally to other parts of the network. By implementing micro-segmentation, organizations can significantly reduce the attack surface and limit the impact of a potential breach.
Centralized Visibility and Log Analytics
Centralized visibility and log analytics are essential for effective security management. Cloud firewalls provide a centralized dashboard that allows security teams to monitor network traffic, detect anomalies, and respond to threats in real-time. They also maintain detailed logs of all traffic and security events, which can be analyzed to identify patterns and trends. This centralized visibility enables organizations to gain a comprehensive understanding of their security posture and make informed decisions about policy changes and threat mitigation strategies.
Use Cases for Cloud Firewalls
Securing Multi-Cloud Workloads
In a multi-cloud environment, organizations leverage multiple cloud providers to optimize performance, cost, and innovation. Cloud firewalls play a crucial role in securing these workloads by providing consistent security controls across different cloud platforms. They can enforce policies to ensure that traffic between different clouds is secure, protecting against threats such as data breaches and unauthorized access. Additionally, cloud firewalls can integrate with cloud-native security tools and services, providing a comprehensive security solution for multi-cloud environments.
Remote Workforce Protection
The rise of remote work has increased the need for robust security solutions to protect remote employees and their devices. Cloud firewalls can be deployed to secure remote access to corporate resources, ensuring that only authorized users can connect to the network. They can also provide application-layer filtering to protect against threats such as phishing attacks and malware infections. By integrating with VPN solutions and other remote access technologies, cloud firewalls can provide a seamless and secure experience for remote workers.
IoT/Edge Computing Security
The proliferation of Internet of Things (IoT) devices and edge computing has introduced new security challenges. These devices often lack robust security controls and can be easily compromised by attackers. Cloud firewalls can be deployed at the edge to provide security controls for IoT devices and edge computing workloads. They can enforce policies to ensure that only authorized devices can connect to the network and can detect and block malicious traffic originating from compromised devices. This helps organizations protect their IoT infrastructure and prevent attacks from spreading to other parts of the network.
DevOps Pipeline Security
In modern software development, DevOps pipelines are used to automate the development, testing, and deployment of applications. However, these pipelines can introduce security risks if not properly secured. Cloud firewalls can be integrated into DevOps pipelines to provide security controls throughout the development lifecycle. They can enforce policies to ensure that only authorized code is deployed, detect and block malicious traffic during testing, and provide real-time monitoring and threat detection during production. This helps organizations ensure that their DevOps pipelines are secure and that their applications are protected from potential threats.
Case Studies: Brief Examples from Finance/Healthcare Sectors
Real-world case studies provide valuable insights into the effectiveness of cloud firewalls in different industries. For example, in the finance sector, a major bank deployed a cloud firewall to protect its multi-cloud environment. The firewall provided robust protection against DDoS attacks and zero-day exploits, ensuring that sensitive financial data remained secure. Additionally, the bank leveraged the firewall's compliance features to meet regulatory requirements such as PCI-DSS. In the healthcare sector, a hospital uses a cloud firewall to secure its IoT devices and edge computing infrastructure. The firewall enforced micro-segmentation policies, limiting the attack surface and protecting patient data from potential breaches. These case studies demonstrate the versatility and effectiveness of cloud firewalls in addressing the unique security challenges of different industries.
Cloud Firewall Best Practices and Considerations
Professional Elements to Highlight
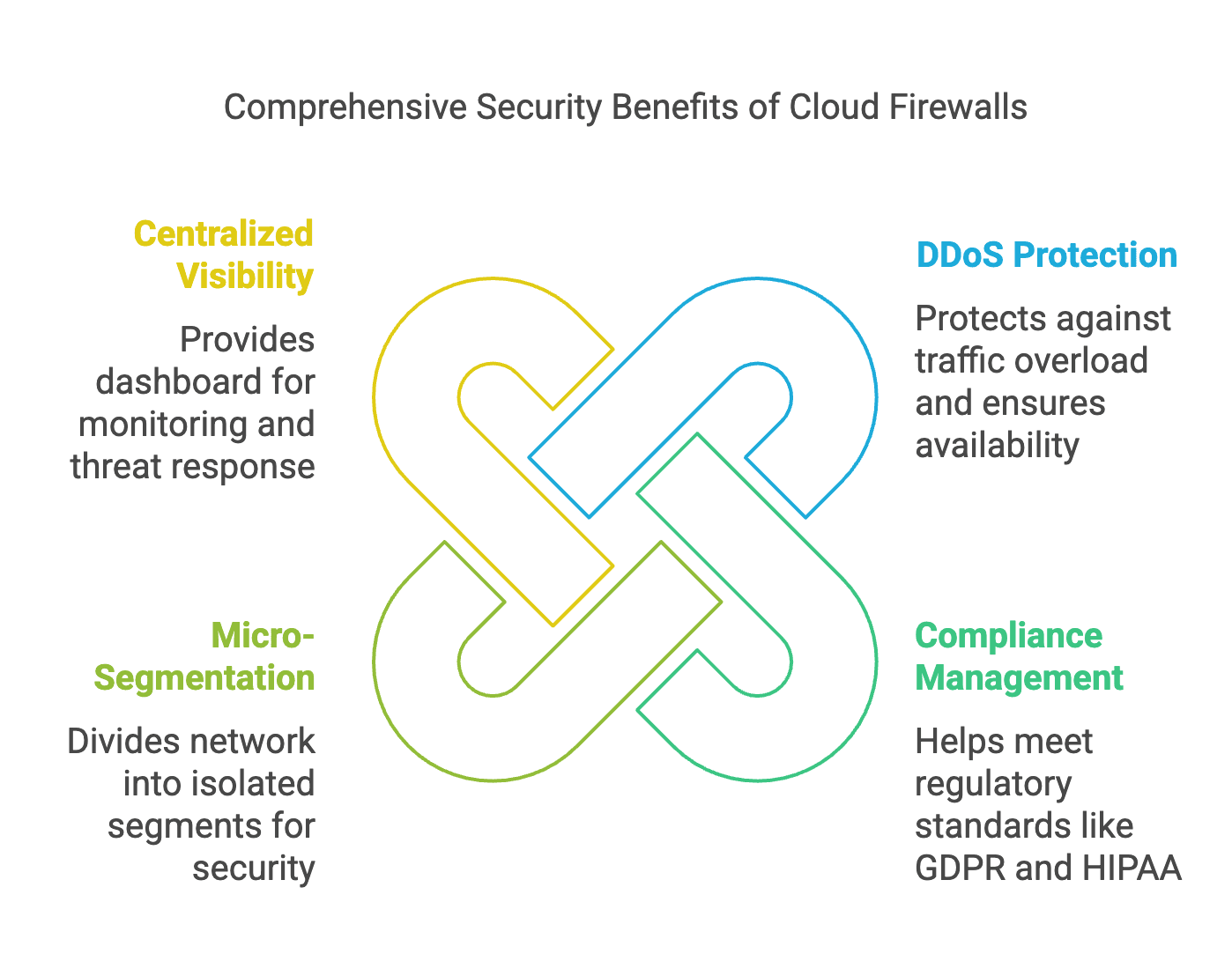
Technical Specifications
When discussing cloud firewalls, it is essential to highlight their technical specifications. Modern cloud firewalls support advanced protocols such as TLS 1.3 for secure communication and IPv6 for next-generation networking. Additionally, they offer robust API integrations, allowing organizations to automate and orchestrate security controls. These technical specifications ensure that cloud firewalls can operate effectively in modern cloud environments and provide the necessary security controls to protect against emerging threats.
Industry Benchmarks
Industry benchmarks such as the Gartner Magic Quadrant and NIST frameworks provide valuable insights into the capabilities and effectiveness of cloud firewalls. Organizations should reference these benchmarks when selecting a cloud firewall solution, ensuring that they choose a product that meets industry standards and best practices. The Gartner Magic Quadrant, for example, evaluates cloud firewall vendors based on their completeness of vision and ability to execute, providing a comprehensive overview of the market landscape. By leveraging these benchmarks, organizations can make informed decisions about their security investments.
Cost Analysis: OpEx vs. CapEx Models for FWaaS
Cost analysis is a critical consideration when deploying cloud firewalls. Organizations must weigh the benefits of OpEx (Operational Expenditure) vs. CapEx (Capital Expenditure) models. Firewall-as-a-Service (FWaaS) solutions typically operate on an OpEx model, where costs are based on usage and subscription fees. This model provides flexibility and scalability, allowing organizations to adjust their spending based on their needs. On the other hand, traditional firewalls often require a CapEx investment, with upfront costs for hardware and software licenses. By analyzing the total cost of ownership (TCO) for each model, organizations can determine the most cost-effective solution for their specific requirements.
Implementation Best Practices
Policy Orchestration with Infrastructure-as-Code (IaC) Tools
Infrastructure-as-Code (IaC) tools such as Terraform, Ansible, and AWS CloudFormation have become essential for modern IT operations. These tools allow organizations to define and manage their infrastructure using code, ensuring consistency and repeatability. When implementing cloud firewalls, it is crucial to leverage IaC tools for policy orchestration. By defining firewall policies as code, organizations can ensure that policies are consistently deployed across different environments and can be easily updated and version-controlled. This reduces the risk of human error and ensures that security policies are always up-to-date.
Performance Optimization: Latency vs. Security Tradeoffs
Performance optimization is a critical consideration when deploying cloud firewalls. Organizations must balance the need for robust security controls with the potential impact on network performance. Latency can be a significant concern, especially in high-traffic environments. To optimize performance, organizations should carefully configure their firewalls to ensure that only necessary traffic is inspected and that policies are optimized for efficiency. Additionally, leveraging cloud-native features such as auto-scaling and elastic rule management can help maintain performance while ensuring security.
Integration with SIEM and SOAR Platforms
Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) platforms are essential tools for modern security operations. Cloud firewalls should be integrated with these platforms to provide a comprehensive view of the security landscape. By sending logs and alerts to SIEM platforms, organizations can gain real-time visibility into security events and detect anomalies. Additionally, integrating with SOAR platforms allows organizations to automate response actions, reducing the time it takes to mitigate threats and minimizing the impact of security incidents.
Future Trends in Cloud Firewalls
AI-Driven Anomaly Detection
Artificial Intelligence (AI) and Machine Learning (ML) are increasingly being used in cybersecurity to detect and respond to threats. Cloud firewalls are no exception. AI-driven anomaly detection can analyze vast amounts of data to identify unusual patterns and behaviors that may indicate a potential threat. This allows organizations to detect and respond to threats in real-time, even if they have never been seen before. AI-driven firewalls can also learn from past incidents to improve their detection capabilities over time, making them an essential tool for future-proofing security.
Convergence with SASE (Secure Access Service Edge)
The convergence of cloud firewalls with Secure Access Service Edge (SASE) is another emerging trend. SASE combines multiple security functions, including firewalls, VPNs, and Zero Trust access controls, into a single, cloud-native platform. This convergence provides organizations with a more holistic approach to security, ensuring that all aspects of network access are protected. By integrating cloud firewalls with SASE platforms, organizations can benefit from enhanced security controls, improved performance, and simplified management.
Quantum-Resistant Encryption in Cloud Firewall Policies
The advent of quantum computing poses a significant threat to current encryption methods. Quantum-resistant encryption is emerging as a solution to ensure that data remains secure even in the face of quantum computing attacks. Cloud firewalls will need to incorporate quantum-resistant encryption into their policies to protect against future threats. This will require the development of new algorithms and protocols that can withstand quantum attacks while maintaining performance and usability.
Conclusion
In conclusion, cloud firewalls have revolutionized modern network security by providing robust, scalable, and flexible security controls tailored for cloud-native environments. Their advanced functionalities, deployment models, and security advantages make them an essential component of any enterprise security strategy. As organizations continue to adopt cloud and computing face increasingly sophisticated threats, cloud firewalls will play a crucial role in ensuring the security and integrity of their IT infrastructure.
EdgeOne offers comprehensive security advantages by integrating advanced security features with edge computing capabilities. It provides robust Web Protection and DDoS protection, effectively mitigating large-scale traffic attacks to ensure service availability. The built-in Web Application Firewall (WAF) defends against common web threats like SQL injection, XSS, and CSRF, safeguarding web applications from malicious requests. Additionally, EdgeOne's intelligent traffic scheduling and edge caching mechanisms optimize content delivery while reducing latency, ensuring a seamless user experience. By combining security and acceleration in a single platform, EdgeOne simplifies management and enhances overall network resilience.
Sign Up to begin your journey with us!
FAQs about Cloud Firewalls
1. What is a Cloud Firewall?
A Cloud Firewall, also known as a Firewall-as-a-Service (FWaaS), is a cloud-based security solution that provides network traffic filtering and monitoring. Unlike traditional hardware firewalls, cloud firewalls are delivered as a service, offering scalable, flexible, and centrally managed protection for both on-premises and cloud-based environments.
2. How is a Cloud Firewall different from a traditional firewall?
Traditional firewalls are hardware-based, deployed at the network perimeter, and require manual management. In contrast, cloud firewalls are software-defined, operate in the cloud, and can be easily managed through a centralized console. They offer greater scalability, flexibility, and the ability to protect distributed environments, including multi-cloud and hybrid architectures.
3. What are the main benefits of using a Cloud Firewall?
- Scalability: Easily scale security resources up or down based on demand.
- Centralized Management: Manage policies and configurations from a single console.
- Flexibility: Protect both on-premises and cloud-based assets seamlessly.
- Advanced Security Features: Offer advanced threat detection, application-layer filtering, and integration with other security services.
- Cost Efficiency: Reduce the need for physical hardware and on-site maintenance.
4. What security features do Cloud Firewalls typically offer?
Cloud Firewalls often include:
- Network Layer Filtering: Basic IP and port filtering.
- Application Layer Protection (WAF): Protection against web application attacks like SQL injection and XSS.
- Intrusion Prevention Systems (IPS): Detection and blocking of known threats.
- Zero Trust Access: Ensuring users and devices are authenticated and authorized.
- Threat Intelligence Integration: Real-time updates on emerging threats.
5. How does a Cloud Firewall protect against cyber threats?
Cloud Firewalls inspect incoming and outgoing traffic to block malicious activities. They can:
- Filter out unauthorized access attempts.
- Detect and block known attack patterns.
- Provide real-time threat intelligence to identify and mitigate emerging threats.
- Enforce security policies across multiple environments.
6. Can Cloud Firewalls integrate with other security solutions?
Yes, Cloud Firewalls are designed to integrate seamlessly with other security solutions such as:
- SIEM (Security Information and Event Management): For centralized logging and threat detection.
- Endpoint Protection: To provide comprehensive security across devices.
- Identity and Access Management (IAM): To enforce zero-trust policies.
- Web Application and API Security (WAAS): For enhanced protection of web applications and APIs.
7. What are the deployment options for Cloud Firewalls?
Cloud Firewalls can be deployed in various ways:
- Cloud-Only Environments: Protecting cloud-based applications and workloads.
- Hybrid Environments: Securing both on-premises and cloud assets.
- Multi-Cloud Environments: Providing consistent security across multiple cloud providers.
8. How do I manage and monitor a Cloud Firewall?
Cloud Firewalls are managed through a web-based console or API, allowing you to:
- Configure security policies.
- Monitor traffic and logs.
- Receive alerts on suspicious activities.
- Generate reports for compliance and auditing.
9. Is a Cloud Firewall suitable for small businesses?
Yes, Cloud Firewalls are scalable and can be tailored to fit the needs of small businesses. They offer cost-effective solutions without the need for significant upfront investment in hardware and maintenance.
10. How can I ensure compliance with regulations using a Cloud Firewall?
Cloud Firewalls help ensure compliance with industry regulations (e.g., GDPR, HIPAA) by:
- Enforcing strict access controls.
- Providing detailed logging and audit trails.
- Ensuring data encryption and secure transmission.
11. What are some common use cases for Cloud Firewalls?
- Protecting Web Applications: Using WAF capabilities to block application-layer attacks.
- Securing Remote Access: Implementing zero-trust access for remote users.
- Multi-Cloud Security: Consistently protecting workloads across multiple cloud platforms.
- Branch Office Security: Centralizing security for distributed locations.
12. How do I choose the right Cloud Firewall for my organization?
Consider the following factors:
- Scalability: Ensure it can grow with your business.
- Integration: Check compatibility with your existing security stack.
- Features: Evaluate the security features offered.
- Support: Look for robust customer support and documentation.
- Cost: Compare pricing models to fit your budget.